How do you set up the 2 step within ASR?Exactly that. Have been using two step verification for quite some time.
-
WANTED: Happy members who like to discuss audio and other topics related to our interest. Desire to learn and share knowledge of science required. There are many reviews of audio hardware and expert members to help answer your questions. Click here to have your audio equipment measured for free!
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Warning: change your password please!
- Thread starter amirm
- Start date
martijn86
Active Member
Go to https://www.audiosciencereview.com/forum/index.php?account/security and check under the Two Factor Authentication header. Never use text messages for authentication though, they can be spoofed. Use an app like Aegis or Authy, or use a hardware key like a Yubikey.How do you set up the 2 step within ASR?
Me too.I didn't even know ASR had 2FA available now. So was good to find that out when changing my password. Have it enabled now.
Just use double step verification, easy and secure.
Ok, so just scrolled through the comments (rather quickly) didn't see the below advice...
If there is a chance passwords have compromised here suggest that not only users change their password here but also
any other site where they may have used the same password
thanks folks!
If there is a chance passwords have compromised here suggest that not only users change their password here but also
any other site where they may have used the same password
thanks folks!
changed
well at least asdf is safe bet, for now..Damn! You just let the cat out of the bag. Now I have to change mine!
Cheers for the prompt heads up Amir, much appreciated.
Sounds like the site is being targeted but it is only being hit on an individual-by-individual level thus far. I trust only a salted hash is stored behind the scenes, rather than our whole passwords, to limit impact if there were a data breach?
Sounds like the site is being targeted but it is only being hit on an individual-by-individual level thus far. I trust only a salted hash is stored behind the scenes, rather than our whole passwords, to limit impact if there were a data breach?
Just remember to keep it in the drawer, and don’t use one with this on the cover:Thats actually the safest way to keep passwords.
Even if somebody breaks into your home, the last thing he is going to look for is notepad with your passwords
Nango
Major Contributor
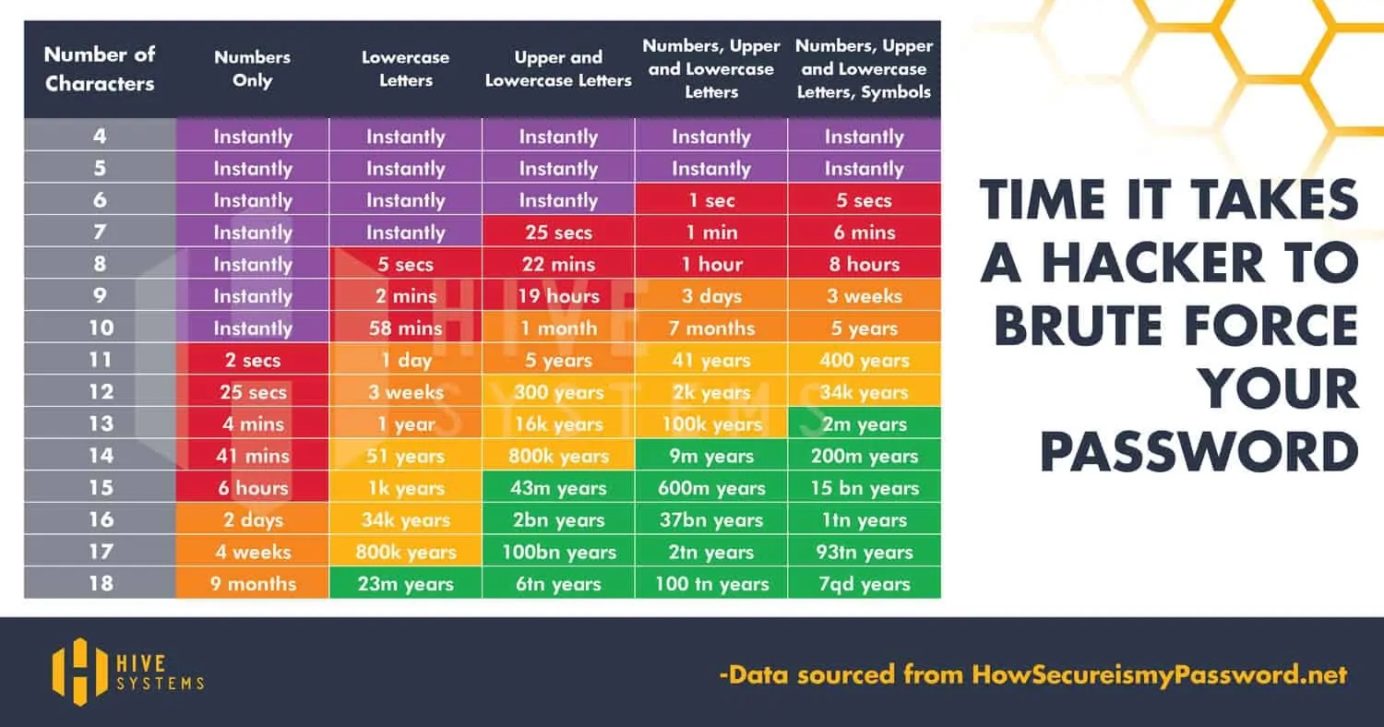
Is this standard with the "+", does it apply everywhere???Also, adding a year and/or an exclamation mark at the end isn't going to save you.
Normally (if you're not a specific target) they just run the 10K most popular passwords (available to the public on GitHub) and a script that tries all the variations on those with capitals, numbers and special characters added. That's automated guessing and pretty fast, it'll give you some positives from a large database.
If you are a specific target because your account has greater value, trying to crack a password becomes an option. They'll try to brute-force all possible combinations of characters. On top of not being easy to guess, the length of a password now becomes important. Every extra character increases the number of possibilities exponentially. If we only count for letters, 26*10⁴ combinations are a lot faster to crunch than 26*10⁸. That's why passphrases are pretty effective if you need a long password that you can remember.
Control leaked e-mail. The easiest scam is just spamming a leaked e-mail address. No password involved. You can add a note to the e-mail adress you use to make an account. For example [email protected] has +asr added. The e-mail is still being delivered to [email protected]. However, if you get spam, you can see where is is directed to. If it is directed to +asr, ASR had willingly or unwillingly leaked your e-mail address. You can simply block all mail that's directed at the +asr combo, notify the sites owner and register a new e-mail (+asr2 for example) at the website.
For non specific targets, if your password is compromised as well, they'll likely try to login to your PayPal with the +asr e-mail. Even if your password isn't unique, that'll fail. But please, use unique passwords!
If you're the type of Audio enthousiast who has a NAS or home server to store their music, you can host your own Bitwarden server with Vaultwarden. This way your data is stored locally with open source software.
Safe browsing!
theREALdotnet
Major Contributor
- Joined
- Mar 11, 2022
- Messages
- 1,208
- Likes
- 2,083
Unless you are like me, whose login is hijacked by someone who were selling equipment through my profile…Life is short. Two Factor is for things that are very important, not for forums and such IMO. Just get a good, unique password and then just breeeeeathe.
FYI Alert: Additional Accounts have been compromised. When identified we Perm Ban the account. For any members who have been compromised. Once you have regained ownership of your computer security. Send an Email to Amir at [email protected]
Include your ASR Username and the email address you used to register your account, if different from the account you send the email with. Amir will reset your password and provide you instructions on how to regain control over your account.
Good luck to those affected.
Include your ASR Username and the email address you used to register your account, if different from the account you send the email with. Amir will reset your password and provide you instructions on how to regain control over your account.
Good luck to those affected.
After changing my password I've checked my last messages to see if someone is selling cooking ware with my account.Unless you are like me, whose login is hijacked by someone who were selling equipment through my profile…
Good luck to everyone. Be safe, be aware...
HarmonicTHD
Major Contributor
- Joined
- Mar 18, 2022
- Messages
- 3,326
- Likes
- 4,837
Hah. Next time I have a brain fart and post BS I have a good excuse - musta been hacked.
- Joined
- Jan 1, 2020
- Messages
- 1,366
- Likes
- 2,054
openssl rand -base64 20
Yup that’ll do!!
Yup that’ll do!!
Similar threads
- Replies
- 8
- Views
- 494
- Replies
- 15
- Views
- 2K
- Replies
- 13
- Views
- 1K
- Replies
- 12
- Views
- 635
- Replies
- 24
- Views
- 1K
D